Hikvision has been designated as a Common Vulnerability and Exposures (CVE) Numbering Authority (CNA). This appointment enables the hi-tech security solutions provider to assign CVE identifiers to flaws reported.
As of 10 February 2018, Hikvision can assign CVE identifiers to vulnerabilities found in its own products and firmware, regardless of whether the issues have been disclosed by Hikvision employees or third-party experts. This is the first step towards vulnerabilities disclosure, verification and solutions release, and the appointment will help speed up the problem-solving process for potential security risks. The announcement is a vote of confidence in Hikvision from within the industry, indicating that the company has gained international recognition not only for the way it handles vulnerabilities and exposures efficiently and effectively, but also for its attitude of being transparent and accountable at all times.
“We are honoured to become a CNA and will keep collaborating with MITRE, to deal with potential security vulnerabilities in a timely and efficient manner,” said Bin Wang, Chief Officer at Hikvision Network and Information Security Laboratory and Network Security Department. “The CNA appointment will help iron out the creases in the information exchanges between security researchers and security solution providers. This will result in end users enjoying meaningful and timely assistance with tackling cyber security issue.”
“Our support of the cyber security vulnerabilities disclosure practices is driven by our deep-seated commitment to supporting and empowering the commercial and civil communities,” Daniel Huang, Hikvision Oceania Managing Director, remarked. “Our goal is twofold: help improve and mature the security practices based on Hikvision solutions provided over the years, and continually keep end-users in the loop, so they can stay informed of the potential risks and have timely solutions to solve those issues.”
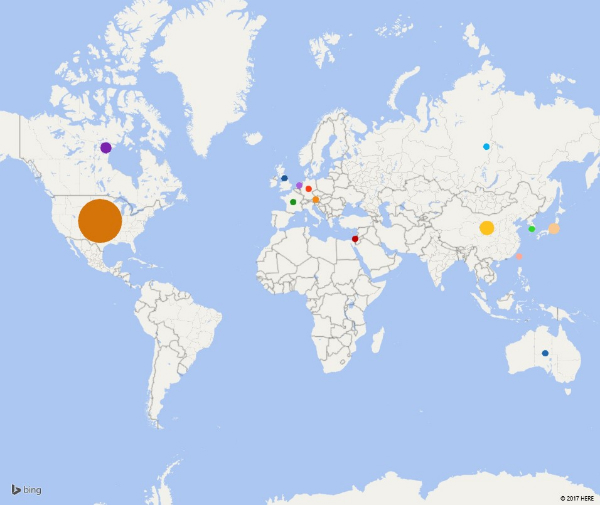
CNAs are organisations from around the world that are authorised to assign CVE Entries to vulnerabilities affecting products within their distinct, agreed-upon scope, for inclusion in first-time public announcements of new vulnerabilities. CNAs are the main method for requesting a CVE ID. Apart from Hikvision, there are 80+ organizations currently participating as CNAs. The list includes Facebook; Google; Apple; IBM; Intel; Airbus; Alibaba; Microsoft; Adobe; BlackBerry; Cisco; Netflix; Oracle; Rapid 7; Schneider Electric; Siemens; HP; CERT/CC; Check Point; Debian GNU/Linux; Dell EMC; HackerOne; ICS-CERT; OpenSSL and MITRE (primary CNA).
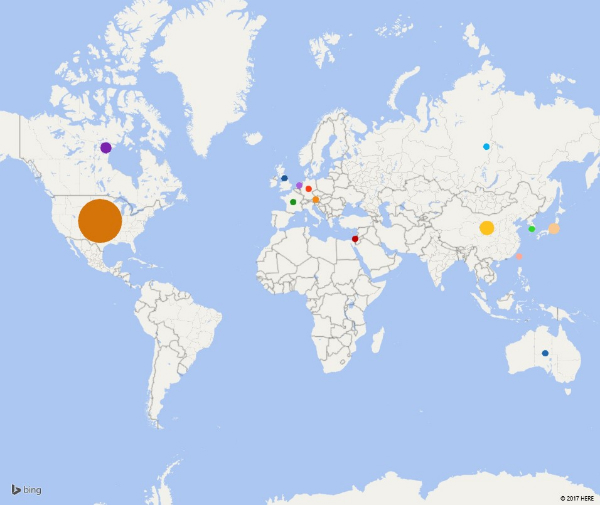
CNAs World Map as of February 2018
About CVE
Launched in 1999, CVE (www.cve.mitre.org) is now the industry standard for vulnerability and exposure identifiers. CVE is sponsored by US-CERT in the office of Cybersecurity and Communications at the U.S. Department of Homeland Security. The CVE List has been copyrighted by MITRE, who is operating as DHS's Federally Funded Research and Development Center (FFRDC). CVE Entries — also called "CVEs," "CVE IDs," and "CVE numbers" — provide reference points for data exchange so that cybersecurity products and services can speak with each other. CVE Entries also provides a baseline for evaluating the coverage of tools and services so that users can determine which tools are most effective and appropriate for their organisation’s needs. Products and services compatible with CVE provide better coverage, easier interoperability and enhanced security.
 Új termékek
Új termékek